An Information Technology (IT) security audit evaluates the security posture of your organization’s IT systems, infrastructure, applications, policies, procedures, processes, and data. It examines these aspects against industry-standard practices and the provisions of different regulations to identify deviations that could open up security vulnerabilities and non-compliance issues. Based on these findings, you can take the necessary action to improve your overall security and compliance.
Below is the best IT security audit software that made it to our list:
- SolarWinds Access Rights Manager A user access and provisioning platform that enables IT administrators to provision, de-provision, and manage user permissions.
- InvGate Insight An IT asset management tool that provides a unified view of your IT infrastructure, enabling you to identify security gaps in your assets.
- MetricStream An internal audit management tool that can save time and costs while identifying the critical vulnerabilities that exist in your IT infrastructure.
- Hyperproof An automated compliance management platform that centralizes your work and uses automation to keep the evidence up-to-date.
- LogicGate Risk Cloud An internal audit management application that offers a centralized location to track and manage all your audit processes.
- MasterControl A comprehensive audit management platform that helps companies in the Life Sciences industry to navigate regulatory requirements.
In this guide, we will discuss the broad steps involved in an IT security audit and the benefits that come from doing it, along with a list of useful software that can ease the audit process for you.
Steps Involved in an IT Security Audit
The exact audit process depends largely on your organizational goals and what you try to achieve through this audit. That said, every audit will have the following broad steps.
Planning
Before embarking on an IT audit, make sure you have the senior management’s approval.
The first step is planning where you decide the objectives and scope of your audit. Note that these objectives must align with your business goals for maximum benefits. Here are some common objectives for IT security audits.
- Improvement in operational efficiency and employee productivity.
- Enhance the security, reliability, and integrity of your data and systems.
- Protecting your assets from cyberattacks and unauthorized users.
- Optimal use of available resources.
- Compliance with laws and regulations.
You can even have more than one objective for the same audit. Based on your goals, create an audit plan where you lay down the scope of the audit, its duration, the likely resources required, and other pertinent information. Also, decide who is responsible for the audit. Is it an internal team, or do you plan to hire a third-party audit firm? Answers to such questions can provide a concrete structure for your audit.
Implementation
With the objectives in place, it’s time to implement the audit based on your plan. Create teams or assign responsibilities to individuals and have a system in place to track their progress. Make sure to provide access to your assets for the relevant employees and stakeholders involved in the audit.
The implementation can include the following aspects based on your goals.
- Risk management
- Control and system testing.
- Review of existing practices and processes.
- Identifying gaps in compliance.
- Understanding incident management practices and their effectiveness.
During this process, organizations often use IT security audit software to streamline the audit processes and improve their efficiency in identifying gaps.
Reporting
Reporting is the outcome of the audit. It’s a good practice to document findings at every stage. If you’re using IT security audit software, most of them have templates for report generation. You can even customize these templates to include the information you need.
These reports help you know the current security of your IT infrastructure and the existing gaps and vulnerabilities. Using this information, you can decide the next steps to improve your security posture, meet your compliance, and fulfill other organizational outcomes.
Follow-up
The last step that completes your audit process is follow-up. Make sure to come up with well-defined actions that address the issues found during the audit. Also, it’s a good idea to audit your IT infrastructure at least twice a year because of the growing adoption of technology and devices. Also, review the impact of your actions and make the necessary changes if required.
In all, these are the broad steps involved in an IT security audit. As mentioned earlier, using the right software can improve the efficiency and outcome of the audit process while reducing the time and effort involved.
Next, let’s look at some of the best software that can help you achieve the objectives of your IT security audit.
Our Methodology
We evaluated tools on the following aspects to ensure that they have the capabilities to check your IT security and make recommendations to improve it:
- Ability to send alerts and notifications.
- Well-designed dashboards and reports to understand the results of the audit.
- Detailed audit planning and trails.
- Availability of incident and issue management features.
- Automation features to reduce time and effort.
Best IT Security Audit Software
Next, let’s explore the capabilities of the above tools to help you decide the best fit for your organization.
1. SolarWinds Access Rights Manager (ARM)
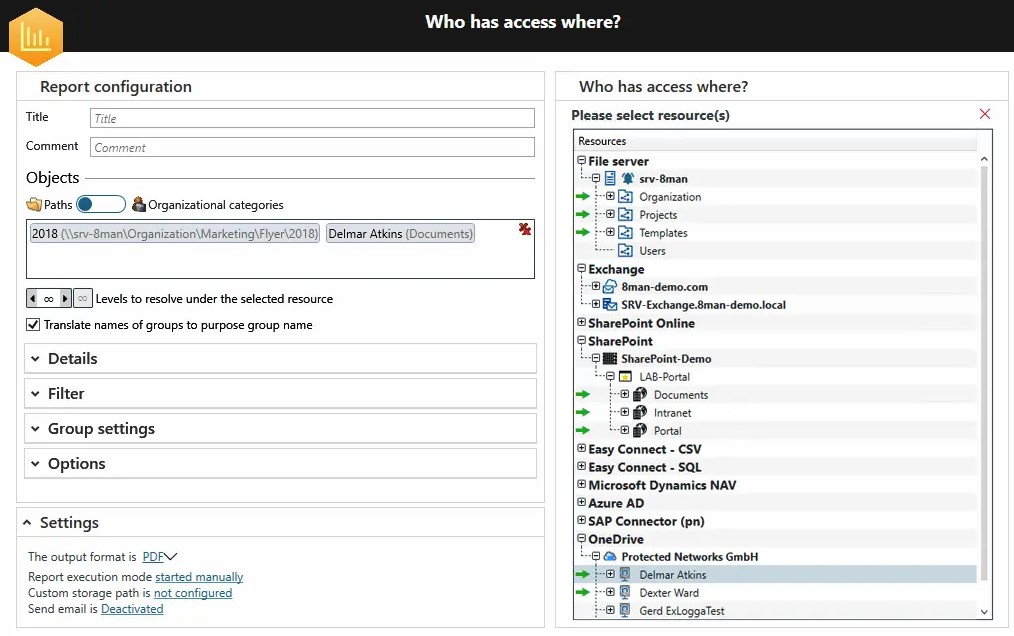
SolarWinds Access Rights Manager is a user access and provisioning platform that streamlines IT security audits by providing insights into user access, monitoring security, and ensuring regulatory compliance with leading standards. Its centralized dashboards reduce the time and effort involved in provisioning access while ensuring visibility.
Source: SolarWinds
Below are SolarWinds’ features that can help with IT security audits.
Comprehensive Visibility
One of the difficult aspects of conducting an audit is to gain visibility into the different systems and their access. SolarWinds ARM eases this difficulty by providing a unified console that provides visibility into all the required information about user access and provisioning. Its centralized user account management can also help with isolating incidents and speed up the remediation process.
Automated Controls
With SolarWinds ARM, you can quickly identify misconfigured permissions and the resulting security threats. Moreover, you can use automated controls to create, modify, delete, activate, and deactivate access to specific files and folders.
Reports and Templates
SolarWinds offers real-time alerts and reports on user activity and permission, and using this information you can respond to attacks like insider threats and potential data leaks. It even comes with many templates that you can customize to check compliance with leading standards.
Overall, SolarWinds ARM is a good choice if a good part of your audit’s focus is on user activity, management, and access controls.
Pros:
- Creates Active Directory reports for easy reference.
- Highly scalable.
- Efficient alerting and reporting capabilities.
- Good customer support.
Cons:
- Implementation can be a bit cumbersome, especially for inexperienced users.
- The GUI can be better.
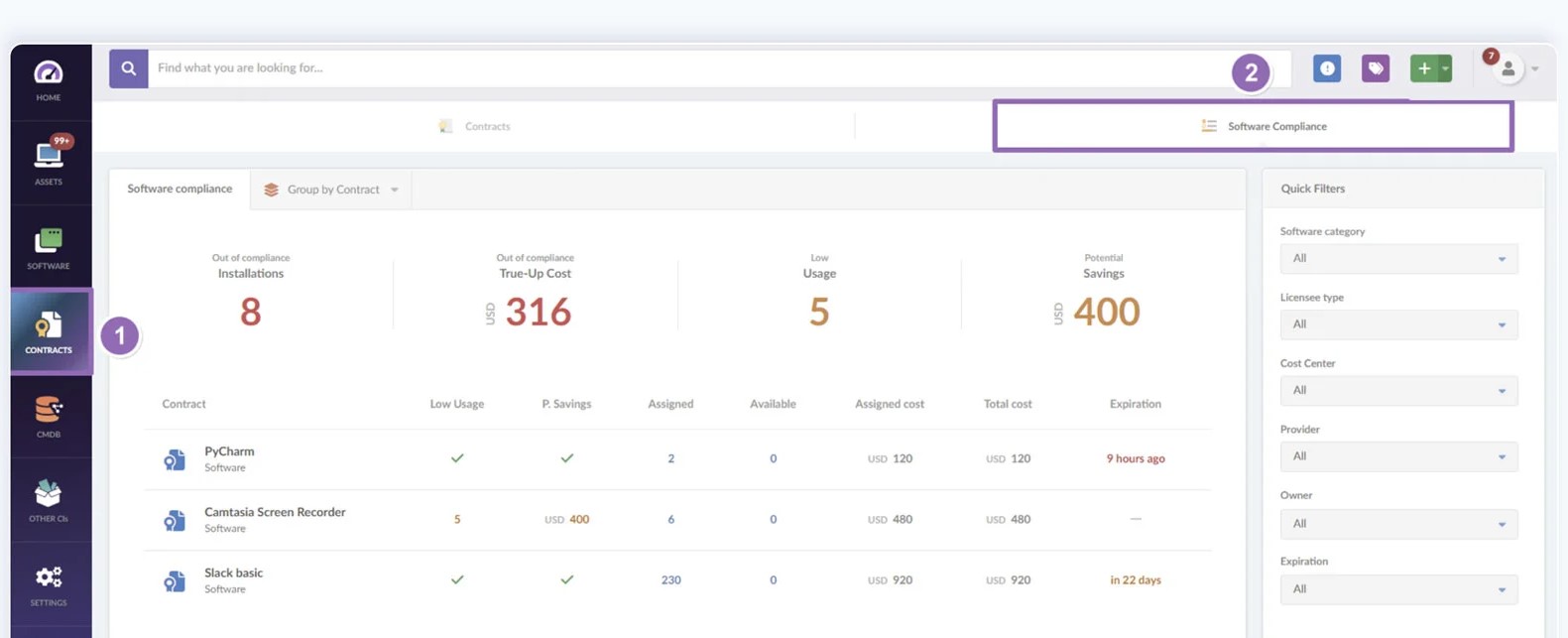
2. InvGate Insight
InvGate is an IT asset management tool that provides a comprehensive view of your IT infrastructure and notifies you of any gaps or issues in it. It also generates comprehensive reports to help you take action when needed.
Source: InvGate
Here’s a look at InvGate Insight’s features that can help with IT security audits.
End-to-end Visibility
InvGate offers end-to-end visibility into your IT assets to help you understand how your systems and processes work together. You can even track the data flow and in the process, identify the gaps that could exist in the implementation. Moreover, you can also find ways to optimize your operations and reduce downtimes.
Risk Management Automation
With InvGate, you can identify the potential items that can open a backdoor for cyberattacks. For example, the use of outdated or unauthorized software can pose a security risk for your organization. Insight can identify these risks automatically, so you can remediate them.
Compliance Checks
InvGate can check every aspect of your IT infrastructure and cross-reference them with compliance requirements to point out gaps. It also reports on non-compliant installations to save you money on potential fines. Its reports and customizable dashboards also ensure the easy identification and fixing of non-compliant items.
Overall, InvGate Insight can provide the required control and visibility into your infrastructure while checking for compliance.
Pros:
- Unified view of all IT assets.
- Streamlined change and configuration management.
- A well-designed user interface.
- Good customer support.
Cons:
- Steep learning curve.
- No option for remote deployment and vulnerability control.
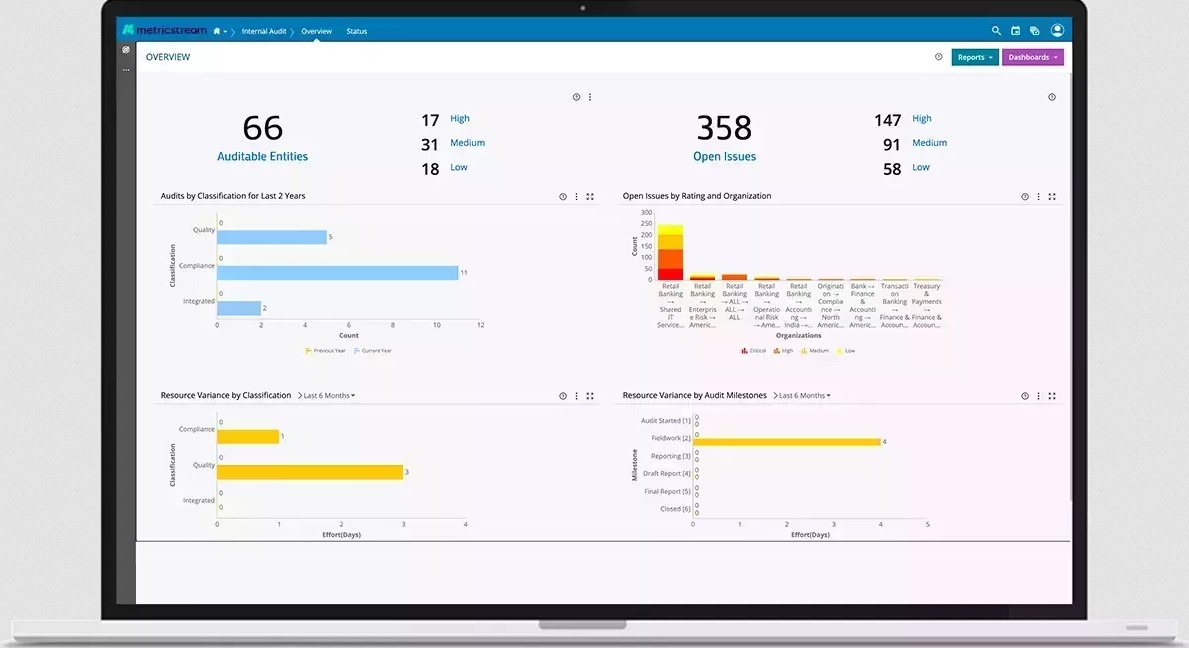
3. MetricStream
MetricStream is an internal audit software for identifying the risks in your IT infrastructure. It leverages advanced technologies like AI to gain greater insights from your data, enhance productivity, and provide actionable items that can improve your business performance.
Source: MetricStream
Let’s look at how MetricStream’s features can help with your audits.
Comprehensive Audit Management
MetricStream maintains all the auditable entities in your audit environment like your business processes, risk library, and more. As a result, you can define complex auditable structures and manage the relationships between different entities easily. Furthermore, updating these entities can be seamless as well.
Improved Collaboration
With MetricStream, you can create extensive audit plans that include defined objectives, scope, resources required, and even the auditors and their responsibilities. A highlight is that you can collaborate all this data in a single platform for making changes when needed.
Audit Reporting
MetricStream creates reports to track the issues identified during the audit and even provides actionable data on how you can address them. Moreover, it provides a list of approvals in a configurable format for easy implementation. Its dashboards are also comprehensive and provide insights into the problem areas.
In all, MetricStream is a handy tool for conducting internal audits to ensure the security of your IT infrastructure.
Pros:
- Supports a common repository of GRC objects.
- Offers incident management.
- Easy to navigate.
- Sends real-time notifications.
Cons:
- Limited out-of-the-box integrations.
- Limited reports.
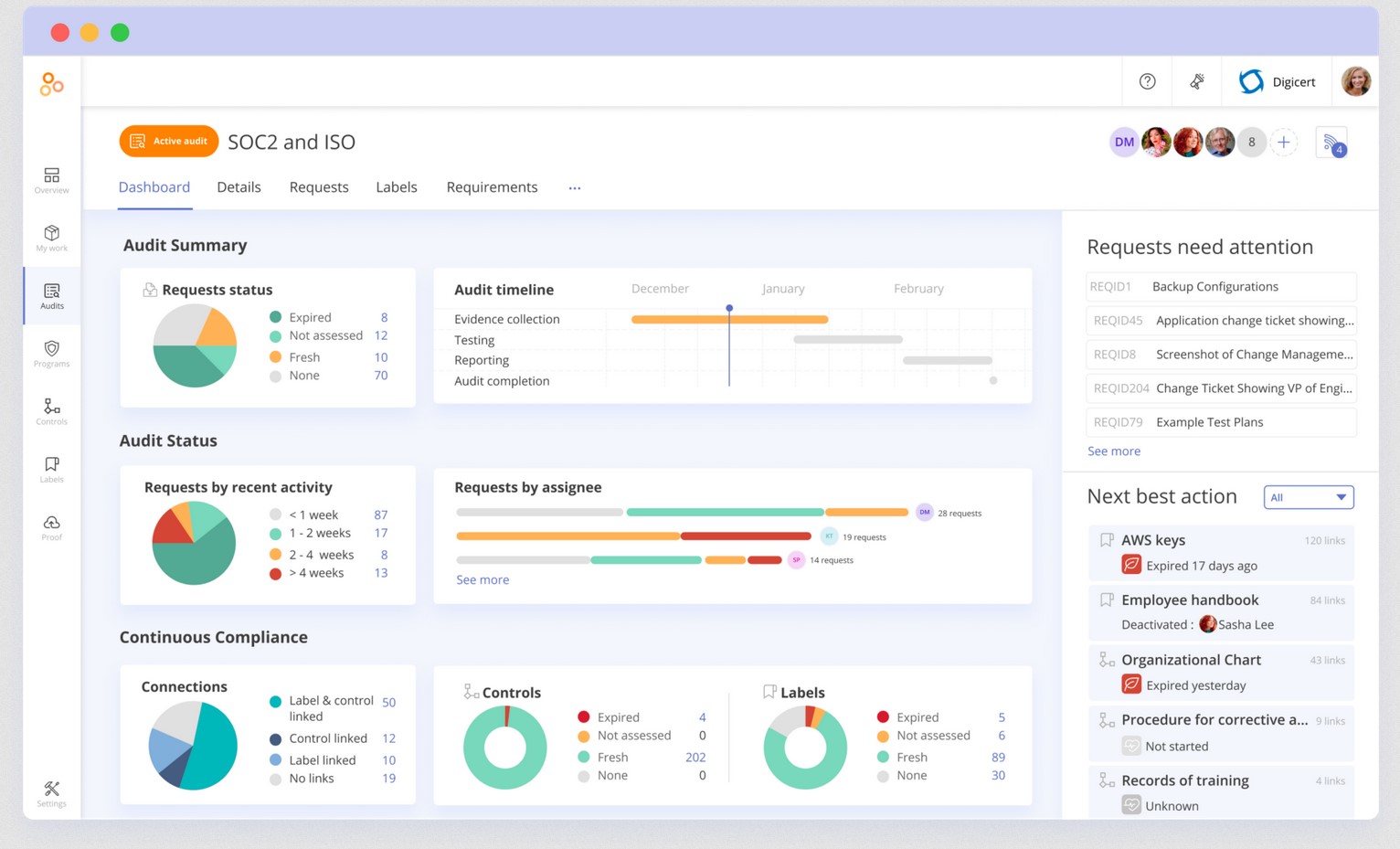
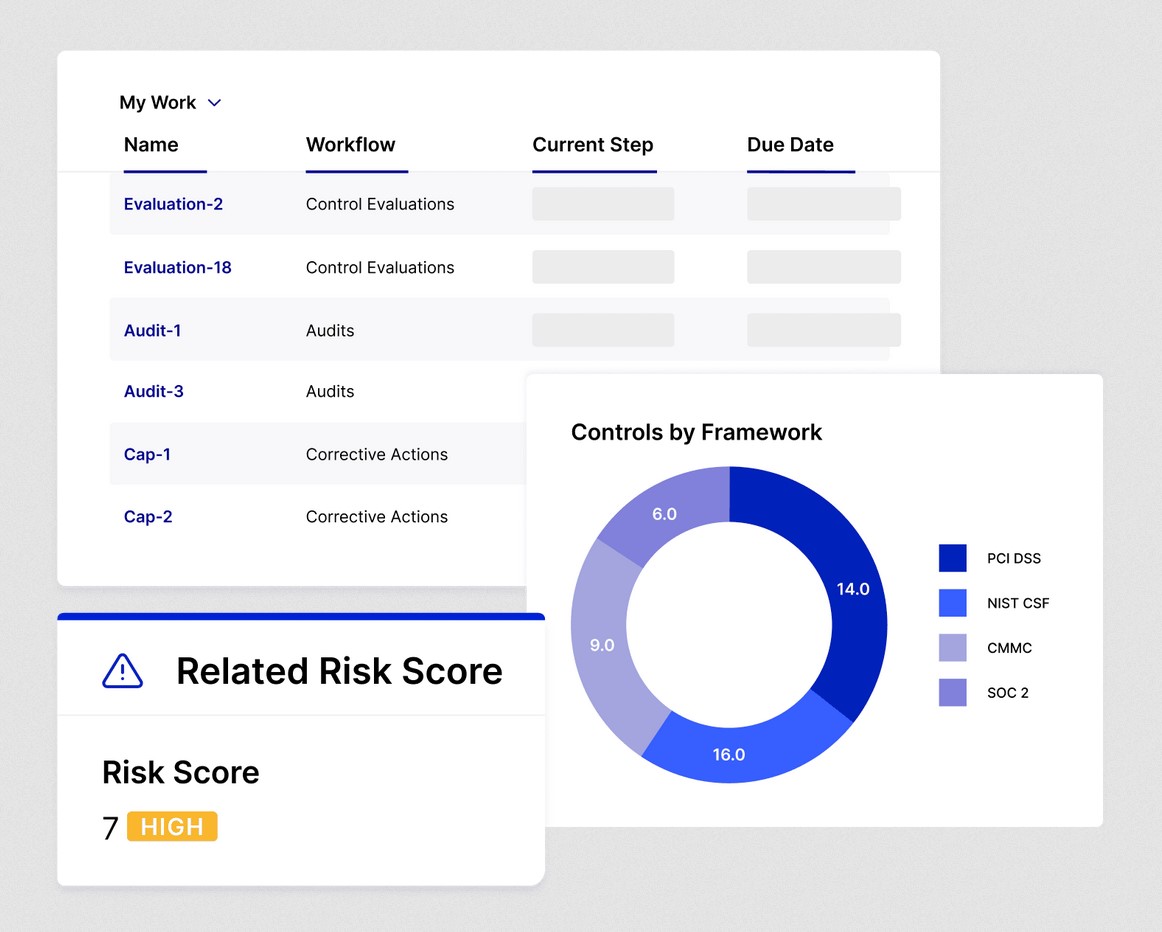
4. Hyperproof
Hyperproof is an automated compliance management tool that offers comprehensive audit management to help meet compliance and boost your IT security. It centralizes all your work in a single pane to offer extensive visibility into the audit process and its outcomes. Also, it uses automation to keep your evidence up-to-date.
Source: Hyperproof
Below are Hyperproof’s features that can handle your audit.
Compliance Mapping
Hyperproof identifies the overlapping requirements of all your compliance standards and maps them with your controls. This approach makes it easy to check for deviations and non-compliance along with the context for these gaps. Using this information, you can quickly fill the gaps.
Evidence Gathering
One of the pain points in an audit is gathering evidence from different stakeholders. Hyperproof’s single dedicated system eases this process, as it enables auditors to raise requests and assign them to stakeholders. In turn, the assigned individuals or teams can upload the evidence. This process creates accountability and transparency for everyone.
Collaboration Across Teams
In today’s remote world, your audit team can be spread across multiple locations and time zones, and Hyperproof enables everyone to seamlessly collaborate on a single audit. It offers a unified and secure means of communication and task management where everyone knows their tasks and completes them.
With such capabilities, Hyperproof makes your audits less overwhelming and more relevant.
Pros:
- The entire platform is user-friendly.
- Automates many audit processes.
- Ensures compliance with leading standards like SOC 2 and ISO 27001
- Organizes documentation.
Cons:
- Reporting can be better.
- Limited integrations.
5. LogicGate Risk Cloud
LogicGate Risk Cloud provides a connected view of risks, controls, and evidence to reduce your time to audit and make the entire process more effective for your organization. It is an internal audit solution that identifies issues and fixes compliance gaps before they are flagged by external auditors.
Source: LogicGate
Let’s look at LogicGate’s features that can help with your internal audits.
Automated Evidence Collection
With LogicGate, you can automate the control notifications and even link relevant evidence with each control. Such a centralized approach makes it easy to track evidence, and the Risk Cloud Documents module will use this data to automatically generate reports.
Corrective Plans
Based on the findings in your audit, LogicGate makes a set of recommendations to fill the gaps and take corrective actions. Accordingly, you can prioritize the action items and implement them to ensure compliance and reduce risks.
Pre-built Dashboards and Reports
LogicGate comes with many pre-built dashboards and reports to help track information about the status of each audit, its findings, the recommended corrective actions, and the progress made on each action. Sharing these key metrics drives stakeholder engagement and support, making your audits even more effective.
Overall, LogicGate automates the many processes involved in internal audits to save time and improve its overall effectiveness.
Pros:
- Highly customizable.
- It supports automation across multiple processes.
- Responsive customer support.
- Seamless integration through APIs.
Cons:
- The user interface can be confusing.
- Steep learning curve.
6. MasterControl
MasterControl is a quality audit management software that automates many tasks in the audit process to ease the process of complying with internal and external regulations. It simplifies the audit planning process and ensures compliance with the U.S. Food and Drug Administration (FDA)’s requirements. This tool is designed for Life Sciences companies to perform laboratory, clinical, and quality audits.
Source: MasterControl
Below are MasterControl’s audit features.
Complete Documentation
MasterControl’s audit management system integrates seamlessly with your Quality Management System (QMS) to create and maintain documentation throughout the audit process. It also makes it easy to find the information you need and use the documents as evidence for compliance.
Extensive Compliance
The highlight of MasterControl is its support for a wide range of compliance standards like FDA, GxP, and ISO. It even provides many automated processes to reduce your time and effort while ensuring compliance with these stringent standards.
Planning and Budgeting
Creating an audit plan and budgeting for it are the initial hiccups that companies face, and MasterControl supports across both these areas. It offers many customizable templates that can act as a good starting point while its automation ensures that you can stay within your budgets and timelines.
Overall, MasterControl is a handy audit management platform for industries operating in the Life Sciences industry.
Pros:
- Easy to set up and use.
- Seamlessly integrates with QMS to create excellent documentation.
- Proactive customer service.
- Helps to comply with stringent regulations like the FDA.
Cons:
- Report generation can be better.
- It offers only limited training and documentation.
Contact the support team to know more.
Thus, these are some of the best IT security audit software that improves the security of your IT infrastructure while helping you maintain compliance with leading standards. That said, not all platforms are suitable for all organizations. Hence, decide what you need and look for a platform that fits your requirements, though the platforms we discussed in this guide meet our listed criteria.
Final Words
IT security audits are essential in today’s business world to protect your IT infrastructure from malicious attacks. These audits identify the existing vulnerabilities and provide contextual information about them, using which you can plug in these gaps before they are exploited by hackers. Moreover, such a proactive approach can help with compliance as well.
In this guide, we looked at the broad processes involved in IT security audits followed by a detailed review of the best IT security audit software. We hope this information helps you pick the right platform that boosts your infrastructure’s resilience, efficiency, and security.